
正文
nginx 配置https 负载均衡
 小程序:扫一扫查出行
小程序:扫一扫查出行【扫一扫了解最新限行尾号】
复制小程序
1、Winodw安装openssl工具(生成SSL证书用的)免编译版本下载:
http://slproweb.com/products/Win32OpenSSL.html
注意:如果openssl在使用过程中报无法读取conf文件,重启下电脑就好了
Cmd里面的全部命令:
C:\OpenSSL-Win64>cd bin
C:\OpenSSL-Win64\bin>openssl genrsa -des3 -out ssd.key 1024
Generating RSA private key, 1024 bit long modulus
....++++++
........++++++
e is 65537 (0x10001)
Enter pass phrase for ssd.key: ---123456
Verifying - Enter pass phrase for ssd.key: ---123456
C:\OpenSSL-Win64\bin>openssl req -new -key ssd.key -out ssd.csr
Enter pass phrase for ssd.key: ---123456
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:cn
State or Province Name (full name) [Some-State]:guangdong
Locality Name (eg, city) []:zhuhai
Organization Name (eg, company) [Internet Widgits Pty Ltd]:ssd
Organizational Unit Name (eg, section) []:ssd
Common Name (e.g. server FQDN or YOUR name) []:yuange
Email Address []:1871707128@qq.com
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:123456
An optional company name []:ssd
C:\OpenSSL-Win64\bin>openssl x509 -req -days 36500 -shal -extensions v3_ca -sign
key ssd.key -in ssd.csr -out ssd.crt
unknown option -shal ----这里面错的原因是:sha1不是shal
usage: x509 args
-inform arg - input format - default PEM (one of DER, NET or PEM)
-outform arg - output format - default PEM (one of DER, NET or PEM)
-keyform arg - private key format - default PEM
-CAform arg - CA format - default PEM
-CAkeyform arg - CA key format - default PEM
-in arg - input file - default stdin
-out arg - output file - default stdout
-passin arg - private key password source
-serial - print serial number value
-subject_hash - print subject hash value
-subject_hash_old - print old-style (MD5) subject hash value
-issuer_hash - print issuer hash value
-issuer_hash_old - print old-style (MD5) issuer hash value
-hash - synonym for -subject_hash
-subject - print subject DN
-issuer - print issuer DN
-email - print email address(es)
-startdate - notBefore field
-enddate - notAfter field
-purpose - print out certificate purposes
-dates - both Before and After dates
-modulus - print the RSA key modulus
-pubkey - output the public key
-fingerprint - print the certificate fingerprint
-alias - output certificate alias
-noout - no certificate output
-ocspid - print OCSP hash values for the subject name and public key
-ocsp_uri - print OCSP Responder URL(s)
-trustout - output a "trusted" certificate
-clrtrust - clear all trusted purposes
-clrreject - clear all rejected purposes
-addtrust arg - trust certificate for a given purpose
-addreject arg - reject certificate for a given purpose
-setalias arg - set certificate alias
-days arg - How long till expiry of a signed certificate - def 30 days
-checkend arg - check whether the cert expires in the next arg seconds
exit 1 if so, 0 if not
-signkey arg - self sign cert with arg
-x509toreq - output a certification request object
-req - input is a certificate request, sign and output.
-CA arg - set the CA certificate, must be PEM format.
-CAkey arg - set the CA key, must be PEM format
missing, it is assumed to be in the CA file.
-CAcreateserial - create serial number file if it does not exist
-CAserial arg - serial file
-set_serial - serial number to use
-text - print the certificate in text form
-C - print out C code forms
-md2/-md5/-sha1/-mdc2 - digest to use
-extfile - configuration file with X509V3 extensions to add
-extensions - section from config file with X509V3 extensions to add
-clrext - delete extensions before signing and input certificate
-nameopt arg - various certificate name options
-engine e - use engine e, possibly a hardware device.
-certopt arg - various certificate text options
-checkhost host - check certificate matches "host"
-checkemail email - check certificate matches "email"
-checkip ipaddr - check certificate matches "ipaddr"
C:\OpenSSL-Win64\bin>openssl x509 -req -days 36500 -extensions v3_ca -signkey s
sd.key -in ssd.csr -out ssd.crt
Signature ok
subject=/C=cn/ST=guangdong/L=zhuhai/O=ssd/OU=ssd/CN=yuange/emailAddress=18717071
28@qq.com
Getting Private key --123456
Enter pass phrase for ssd.key: --123456
C:\OpenSSL-Win64\bin>openssl genrsa -des3 -out server.key 2048
Generating RSA private key, 2048 bit long modulus
.........................................+++
...+++
e is 65537 (0x10001)
Enter pass phrase for server.key: ---123456
Verifying - Enter pass phrase for server.key: ---123456
C:\OpenSSL-Win64\bin>openssl req -new -key server.key -out server.csr
Enter pass phrase for server.key: ---123456
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:cn
State or Province Name (full name) [Some-State]:guangdong
Locality Name (eg, city) []:zhuhai
Organization Name (eg, company) [Internet Widgits Pty Ltd]:ssd
Organizational Unit Name (eg, section) []:ssd
Common Name (e.g. server FQDN or YOUR name) []:yuange
Email Address []:1871707128@qq.com
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:123456
An optional company name []:ssd
C:\OpenSSL-Win64\bin>openssl x509 -req -days 36500 -md5 -extensions v3_req -CA s
sd.crt -CAkey ssd.key -CAcreateserial -in server.csr -out server.crt
Signature ok
subject=/C=cn/ST=guangdong/L=zhuhai/O=ssd/OU=ssd/CN=yuange/emailAddress=18717071
28@qq.com
Getting CA Private Key ---123456
Enter pass phrase for ssd.key: ---123456
以上的密码全部都是123456
注意:以上生成的证书保存在openssl/bin目录下,然后把生成的证书拷贝到nginx/conf的目录下,在这里面我只拷贝了server.crt 、server.key

2、什么都配置好后发现:
Nginx -t 编译成功,但是运行的时候就自动关闭了,查看日志的时候报错了:
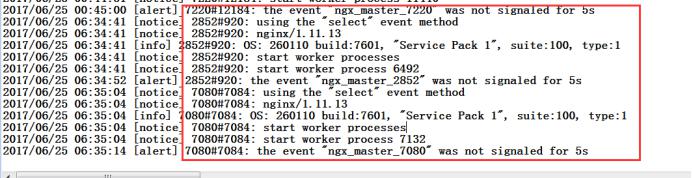
查了好久,终于知道了原因:
Windows下的nginx配置ssl的key是不能存储密码的,否则就会报这个错
解决办法:
在cmd中cd 到openssl/bin的目录下,输入:
Openssl rsa -in C:\OpenSSL-Win64\bin\server.key -out c:/server.key.unsecure
输入server.key当初设置的密码,这里面是123456
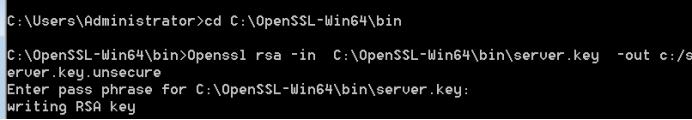
然后在C根目录下可以看到:成功

把server.key.unsecure替换在nginx.conf文件中的server.key内容 即可
3、配置nginx.conf
#使用的用户和组,window下不指定
#user nobody;
#指定工作衍生进程数(一般等于CPU总和数或总和数的两倍,例如两个四核CPU,则总和数为8)
worker_processes 3;
#指定错误日志文件存放路径,错误日志级别可选项为【debug|info|notice|warn|error|crit】
#error_log logs/error.log;
#error_log logs/error.log notice;
error_log logs/error.log info;
#指定pid存放路径
#pid logs/nginx.pid; #工作模式及连接数上限
events {
#使用网络I/O模型,Linux系统推荐使用epoll模型,FreeBSD系统推荐使用kqueue;window下不指定
#use epoll;
#允许的连接数
worker_connections 1024;
} #设定http服务器,利用他的反向代理功能提供负载均衡支持
http {
#设定mime类型
include mime.types;
default_type application/octet-stream;
#设定日志格式
#log_format main '$remote_addr - $remote_user [$time_local] "$request" '
# '$status $body_bytes_sent "$http_referer" '
# '"$http_user_agent" "$http_x_forwarded_for"'; #设定请求缓冲
client_header_buffer_size 1k;
large_client_header_buffers 4 4k; #设定access log
#access_log logs/access.log main;
client_header_timeout 3m;
client_body_timeout 3m;
send_timeout 3m; sendfile on;
tcp_nopush on;
tcp_nodelay on;
#keepalive_timeout 0;
keepalive_timeout 65; #开启gzip模块
gzip on;
gzip_min_length 1100;
gzip_buffers 4 8k;
gzip_types text/plain application/x-javascript text/css application/xml; output_buffers 1 32k;
postpone_output 1460; server_names_hash_bucket_size 128;
client_max_body_size 8m; fastcgi_connect_timeout 300;
fastcgi_send_timeout 300;
fastcgi_read_timeout 300;
fastcgi_buffer_size 64k;
fastcgi_buffers 4 64k;
fastcgi_busy_buffers_size 128k;
fastcgi_temp_file_write_size 128k;
gzip_http_version 1.1;
gzip_comp_level 2;
gzip_vary on; #设定负载均衡的服务器列表
upstream url{
#根据ip计算将请求分配各那个后端tomcat,可以解决session问题
#ip_hash;
#同一机器在多网情况下,路由切换,ip可能不同
#weigth参数表示权值,权值越高被分配到的几率越大
#server localhost:8080 weight=1;
#server 10.152.252.160:8443 weight=2;
#server 10.152.252.162:8443 weight=20;
server 10.152.252.160:8443 max_fails=2 fail_timeout=600s;
server 10.152.252.162:8443 max_fails=2 fail_timeout=600s;
} #设定虚拟主机
server {
listen 8080;
#server_name 10.152.252.160; #proxy_pass https://url;
rewrite ^(.*)$ https://$host:8443$1 permanent;
#charset koi8-r;
charset UTF-8;
#设定本虚拟主机的访问日志
#access_log logs/host.access.log main; #error_page 404 /404.html; # redirect server error pages to the static page /50x.html
#
error_page 500 502 503 504 /50x.html;
location = /50x.html {
root html;
}
}
# HTTPS server
server {
listen 443;
listen 8444;
server_name 10.152.252.160; ssl on;
ssl_certificate server.crt;
ssl_certificate_key server.key.unsecure; ssl_session_timeout 5m; ssl_protocols SSLv2 SSLv3 TLSv1;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on; location / {
root html;
index index.html index.htm; proxy_redirect off;
#保留用户真实信息
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_next_upstream error timeout invalid_header http_500 http_503 http_404;
proxy_max_temp_file_size 128m; proxy_pass https://url;
}
}
}







